This quarter, CERT NZ responded to 1,351 incident reports about individuals and businesses from all over New Zealand. This report shares information around these incidents as well as highlighting examples of work CERT NZ is doing to help. There are two parts to the report:
A Highlights Report focusing on selected cyber security incidents and issues.
A Data Landscape Report providing a standardised set of results and graphs for the quarter.
Highlights
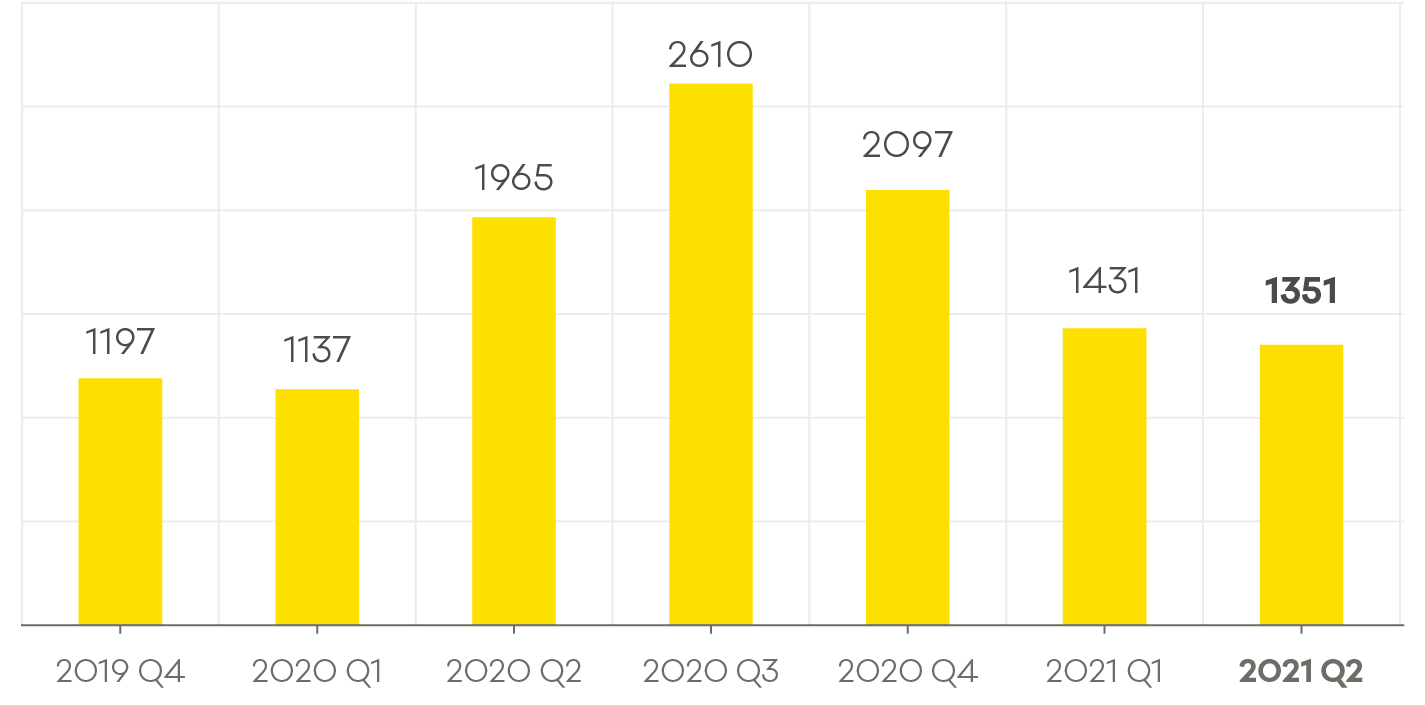
The average number of incident reports per quarter is 1,624 and average direct financial loss per quarter is $4 million. These figures are based on the previous eight quarters
1,351 incidents were responded to by CERT NZ in Q2 2021, down 6% from Q1 2021
$3.9 million in direct financial loss was reported in Q2, a 30% increase from Q1 2021.
Unauthorised access reports increased by 37% from Q1 2021
150% increase in ransomware reports from Q1 2021
Number of incidents responded to
A total of 1,351 incidents were responded to in Q2 2021.
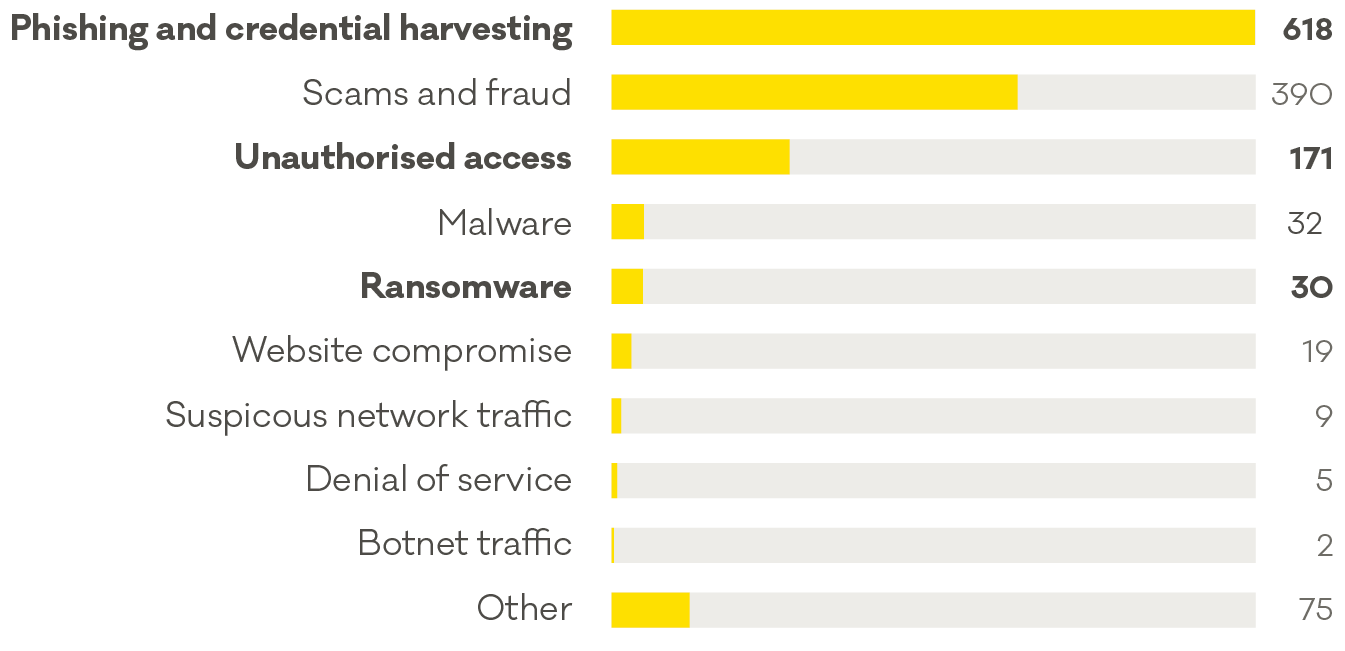
Breakdown by incident category
Phishing and credential harvesting remains the most reported incident category, with 618 reports in Q2, 2021.
Focus area: Ransomware reports continue to rise
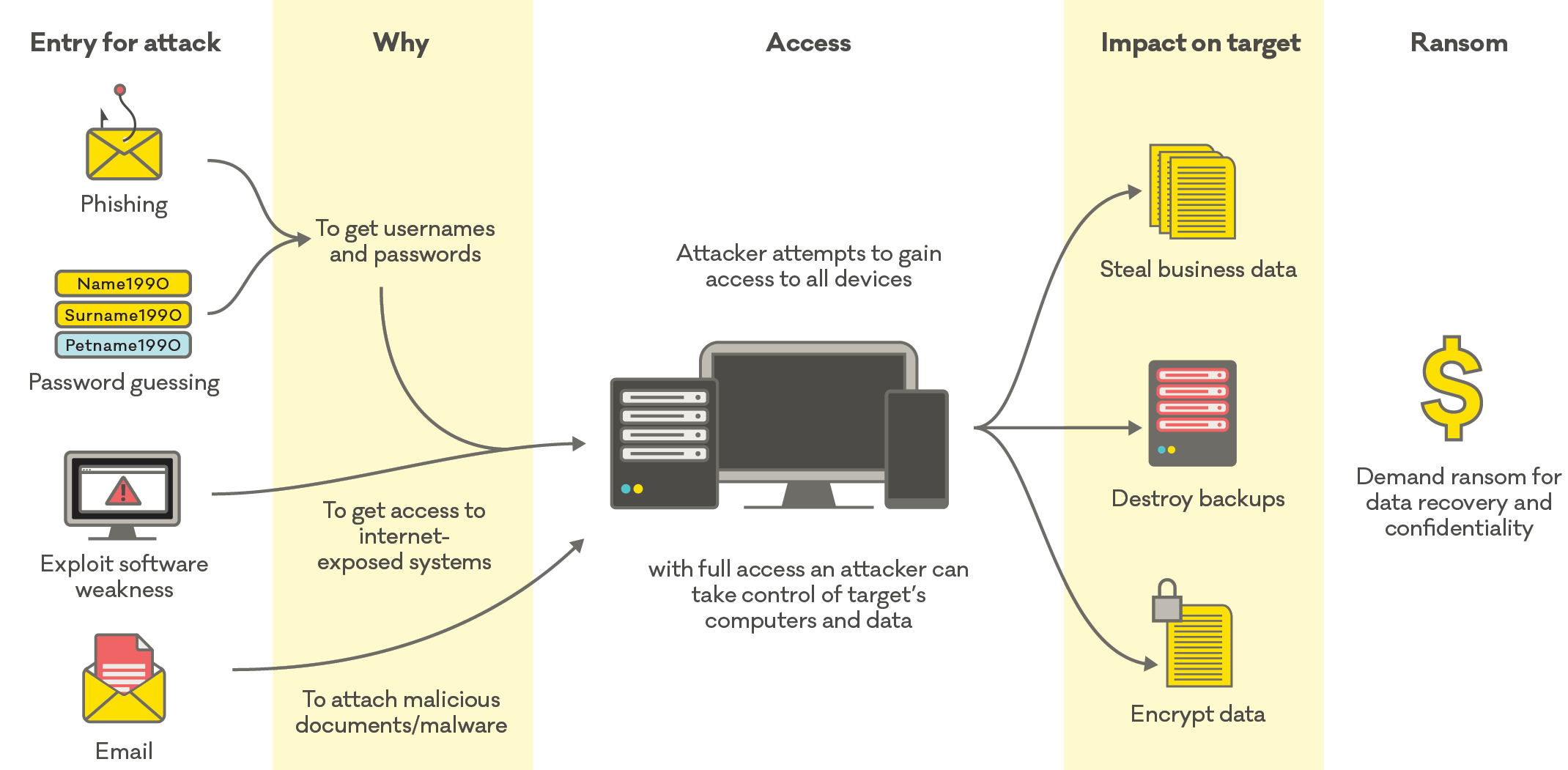
The number of ransomware reports responded to by CERT NZ increased this quarter. There were 30 reports about ransomware in Q2 (up from 12 in Q1), mostly from businesses and organisations.
How ransomware works
What does ransomware look like?
A ransomware attack is accompanied by a README.txt file pop-up or a change to your desktop background. Another indication of a ransomware infection is being unable to access or open any files.
If you’ve been affected
If you receive a ransomware notification, disconnect your computer from your network and isolate the machine to prevent the malicious software spreading further. Simply do this by unplugging your cords and router. Then seek the advice of an IT professional to help investigate which computers are affected, and work out how to get back up and running.
CERT NZ does not recommend paying the ransom. Payment doesn’t guarantee that all your data will be decrypted, and you’ll still likely need IT professional help. It may also open you up to future cyber security attacks as attackers may believe you are willing to pay.
Prevention is key
There are different variants of ransomware, however the motivations and outcomes are the same. Attackers are motivated by financial gain, and recipients are left with encrypted data. The best thing you can do is apply preventative steps.
Be prepared No matter what kind of cyber security incident you face, it’s important to have an incident response and recovery plan. Having a plan and testing it will make it faster and easier to deal with the real thing. If you need some help preparing your incident response plan, follow the step-by-step guide to creating an incident response plan.
Case study: Retailer recovers from ransomware
Businesses and organisations of all sizes are increasingly experiencing the impacts of ransomware compromises, and the impacts are not only financial, as one business experienced.
Insight: Weak and default passwords make for easy targets
Alongside the data from incidents directly reported, CERT NZ also analyses and monitors cyber security information provided by local and international partners. In Q2, CERT NZ identified almost 4,500 brute force incidents involving New Zealand internet-enabled devices like routers and WiFi cameras, where attackers targeted weak or default usernames and passwords.
Protecting your internet-enabled devices
Devices like routers and WiFi cameras often have pre-configured usernames and default passwords. Even if the passwords look strong, they’re often commonly used and attackers can target them.
To protect against brute force attacks, CERT NZ recommends anyone with an internet-enabled device to update the default usernames and passwords where possible, using long, strong and unique passwords. Refer to the device’s user manual for instructions on how to update these settings.
Insight: Cryptocurrency-investment scams on the rise
Cryptocurrency-investment scams made up 13% of the total direct financial loss in Q2, with a total of $500,000. Reports about this type of scam have been steadily increasing, up 50% from last quarter.
