17 December 2021
Department of Internal Affairs (DIA) Digital Messaging Manager Joe Teo said during September and October 2021 the Department received over 114,000 reports to its 7726-reporting service, the highest in the Department’s history.
“This scam is having a significant effect”, said Teo. “It is continuing to have far reaching impacts on New Zealanders with an estimated 400,000 Flubot scam messages being sent each day across all mobile network providers”, said Teo.
CERT NZ, the government’s cyber security watchdog, was also inundated with support calls.
“We were working collaboratively with New Zealand ISPs to protect as many people as possible,” said CERT NZ Director Rob Pope. “We sent out take down request close to 1,200 malicious websites hosting the Flubot malware. Doing this means that there were fewer places for the software to hide.”
CERT NZ were contacted by one individual who fell victim to the scam in early October.
“I was waiting on a parcel delivery for my daughter’s birthday when I got the message and clicked on the link. Next thing I knew I was getting dozens of phone calls and texts from individuals who thought I was a scammer”.
Their number was unknowingly used to forward the scam message to over 548 individuals over the next 3 days.
“I only found out about the Flubot scam when someone from the Department of Internal Affairs contacted me and told me I was impacted. I then got in touch with CERT NZ who helped me complete a factory reset of my phone and thankfully the messages stopped”.
There are currently approximately 200 infected devices across all mobile networks that are still infected with the Flubot scam. These devices will be unknowingly sending thousands of spam messages out to other New Zealanders each day. Individuals impacted by the scam may be receiving large numbers of messages from people receiving the scams from their number.
DIA, the Telecommunications Forum, CERT NZ and the mobile network providers Vodafone, Spark, 2Degrees, and Vocus are working together to encourage the public to be on the lookout for harmful messages.
“Government departments, industry providers and the TCF are working together to reduce the harm of this text scam” said Telecommunications Forum CEO Paul Brislen. He added that New Zealanders had a part to play.
“We encourage anyone whose device is still infected to complete a factory reset immediately to prevent this scam from spreading any further” says Pope.
“If you have been impacted by this scam, you can also help reduce the harm by taking the easy steps to clear your device”.
Pope recommends if anyone discovers they’re affected and needs advice on completing a factory reset, they can contact CERT NZ at cert.govt.nz External Link
Flubot is not the only SMS scam out there.
“If you or anyone you know receives any unexpected or suspicious messages we encourage you to report it to the Department on 7726. By working together and reporting these scams, we can help one another avoid being scammed” says Teo.
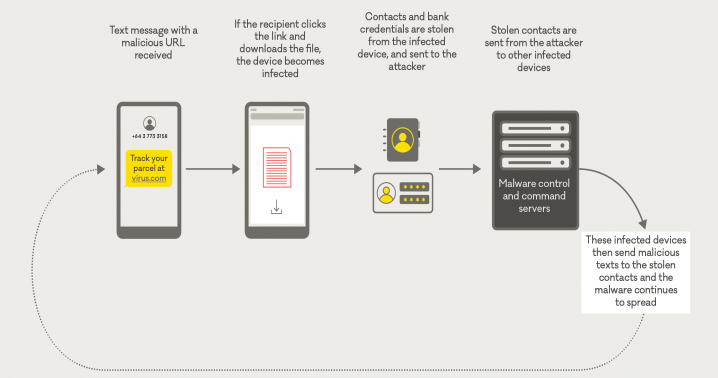
How SMS scam messages work
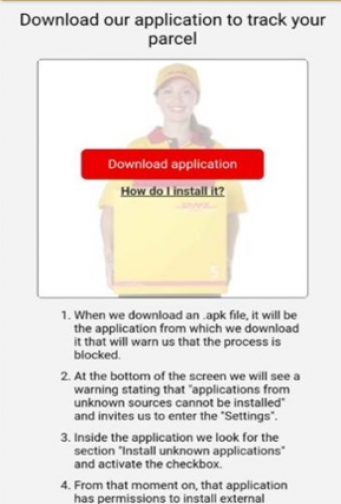
The scam is usually disguised as a legitimate text message about a missed call or parcel delivery with a hyperlink included. This links to a malicious website directing users to download a new application to the phone.
Once downloaded this app will infects the device with the malware which steals personal information including banking details and passwords.
The malware sends the contact details to the scammers and will forward the scam message from the infected device to other people's contacts without the user’s knowledge, further spreading the scam.
What some of the scam messages look like:

How to report a spam message
Text Spam: You can report text spam to the Department of Internal Affairs for free by forwarding the spam text message to 7726 (SPAM).
Email Spam: If the email has no attachments then you can complete a short online form on the Department of Internal Affairs website External Link