This quarter, CERT NZ received 870 incident reports. This is the highest number of reports to date. The reports show that a broad cross section of New Zealanders and organisations are impacted by cyber security issues. They also show a significant increase in both incident type and financial impact compared to Q2.
Some examples include:
- financial losses increased by 35% to $2.9 million
- reports related to scam and fraud were almost double what we saw in Q2. This was due to a large number of webcam scam reports
- reports of unauthorised access increased by 28%
- although we received reports across all age groups, the 65+ age group experienced the highest value of direct financial loss. The total loss for this age group was $930,000 this quarter, compared to $123,000 in Q2.
Results in numbers
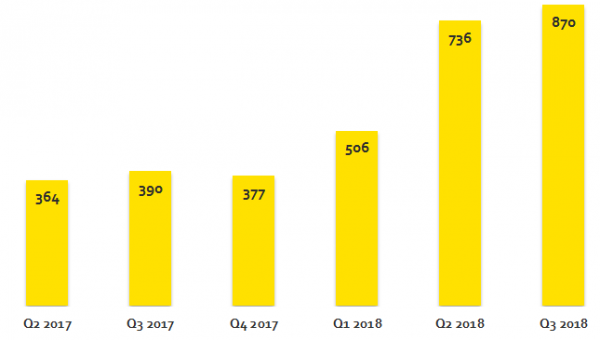
We received 870 reports in the third quarter of 2018.
This is the highest number of incidents reported to CERT NZ since its establishment.
870 incidents
We received 870 incident reports this quarter. This is up 18% from the previous quarter.
Direct financial losses
Direct financial losses increased by 35% this quarter, to $2,993,518.
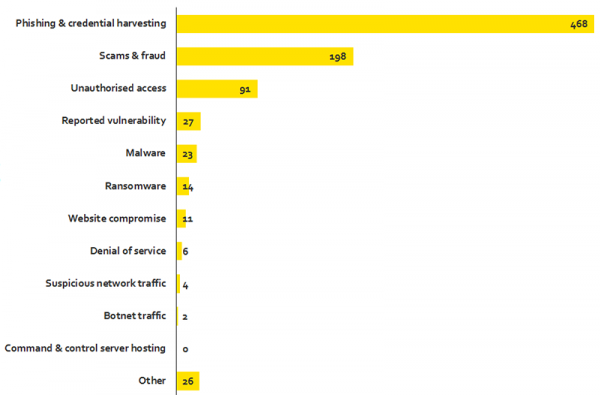
Results by type
Scam and fraud had the highest increase in number of incidents reported this quarter. This jump was led by a large number of webcam scam reports.
198 scam and fraud reports
There were 198 scam and fraud reports in quarter three, a 90% increase from quarter two.
Phishing
Phishing remains the largest category of incidents reported. Reports of these have remained steady compared to last quarter.
Breakdown by incident category
Unauthorised access reports
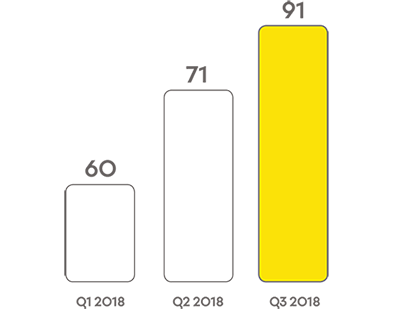
Reports of unauthorised access continue to increase. We received 91 reports this quarter, a 28% increase on quarter two.
More than a third of these reports related to attackers being able to access business and personal email accounts through weak account passwords.
Case study: Business compromise leads to advisory
An IT provider noticed that one of its clients was receiving emails pretending to be a recognised supplier.
The emails contained fake invoices and were attempting to trick the client into paying the invoiced amount into the attacker’s account.