This quarter, CERT NZ responded to 2,333 incident reports about individuals and businesses from all over New Zealand. This report shares information around these incidents as well as highlighting examples of work CERT NZ is doing to help. There are two parts to the report:
Insights report focusing on selected cyber security incidents and issues.
A Data Landscape report providing a standardised set of results and graphs for the quarter.
Highlights
$3.7 million in direct financial loss was reported in Q1. 30% of incidents reported financial loss. A 44% decrease from Q4, 2021.
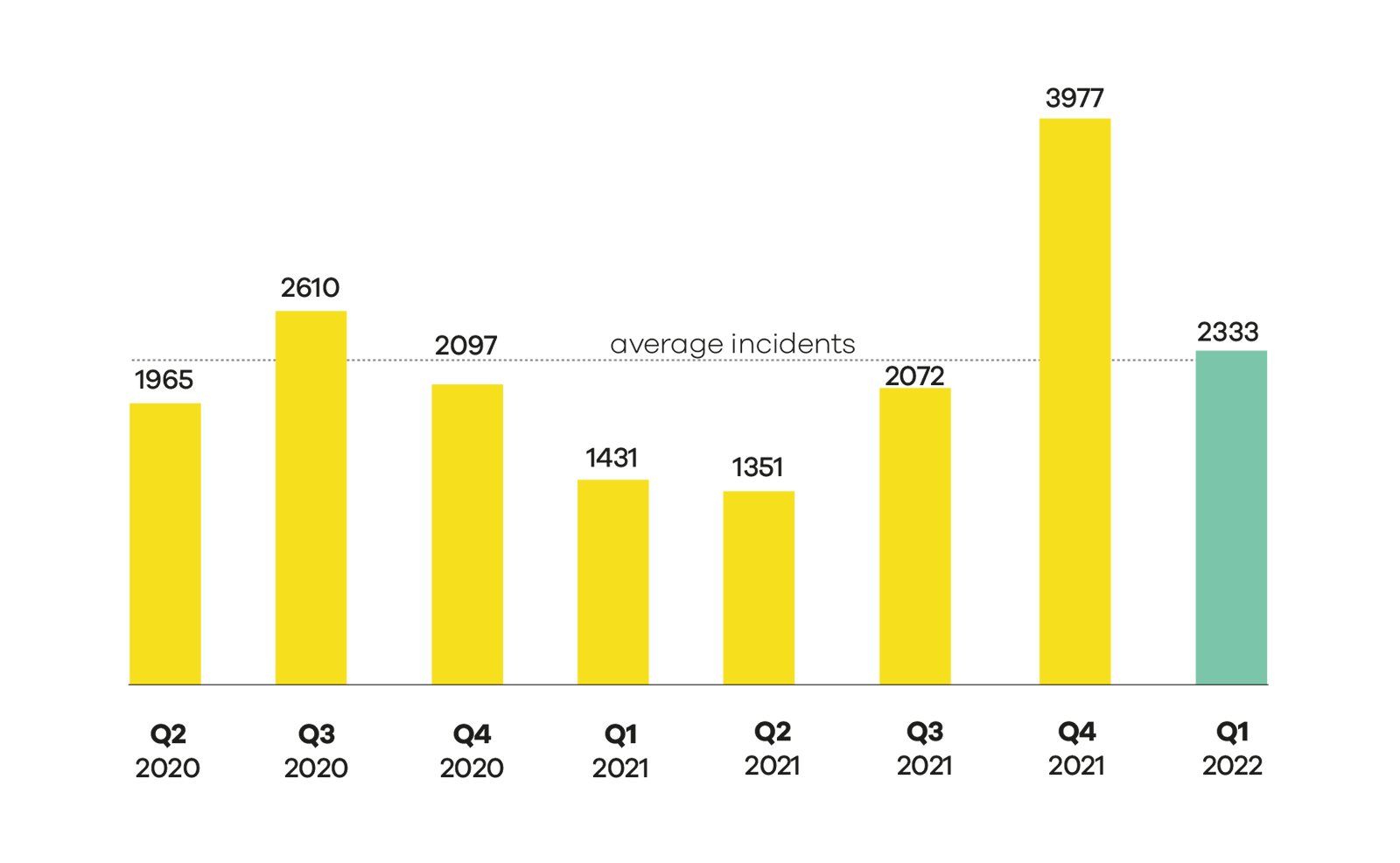
2,333 incidents were responded to by CERT NZ in Q1 2022, down 41% from Q4 2021.
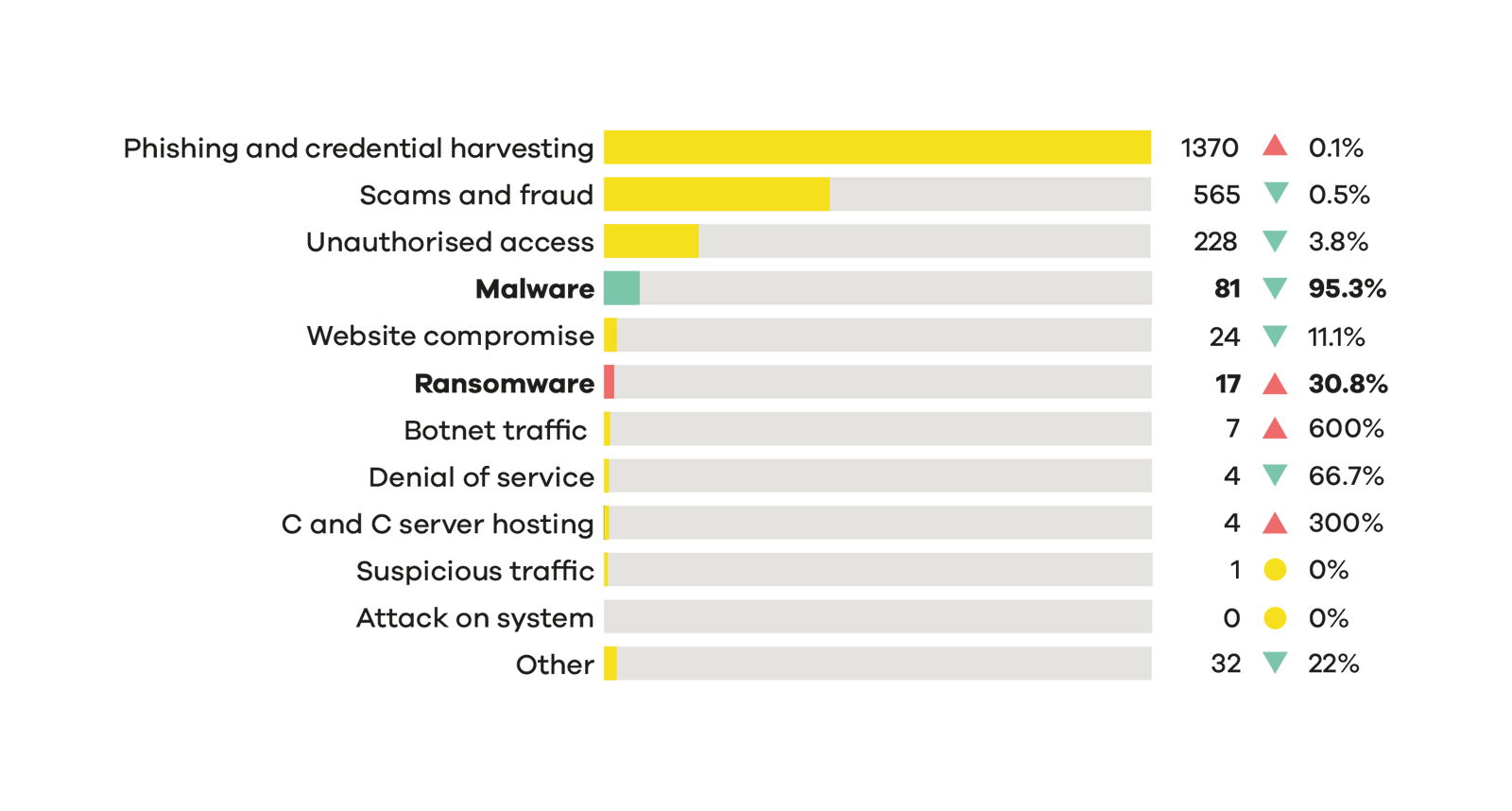
A 31% increase in ransomware reports from Q4, 2021.
95% decrease in malware reports from Q4 2021.
The average number of incident reports per quarter is 2,227 and average direct financial loss is $4 million. These figures are based on the previous 8 quarters.
Number of incidents responded to
A total of 2,333 incidents were responded to in Q1 2022.
Breakdown by incident category
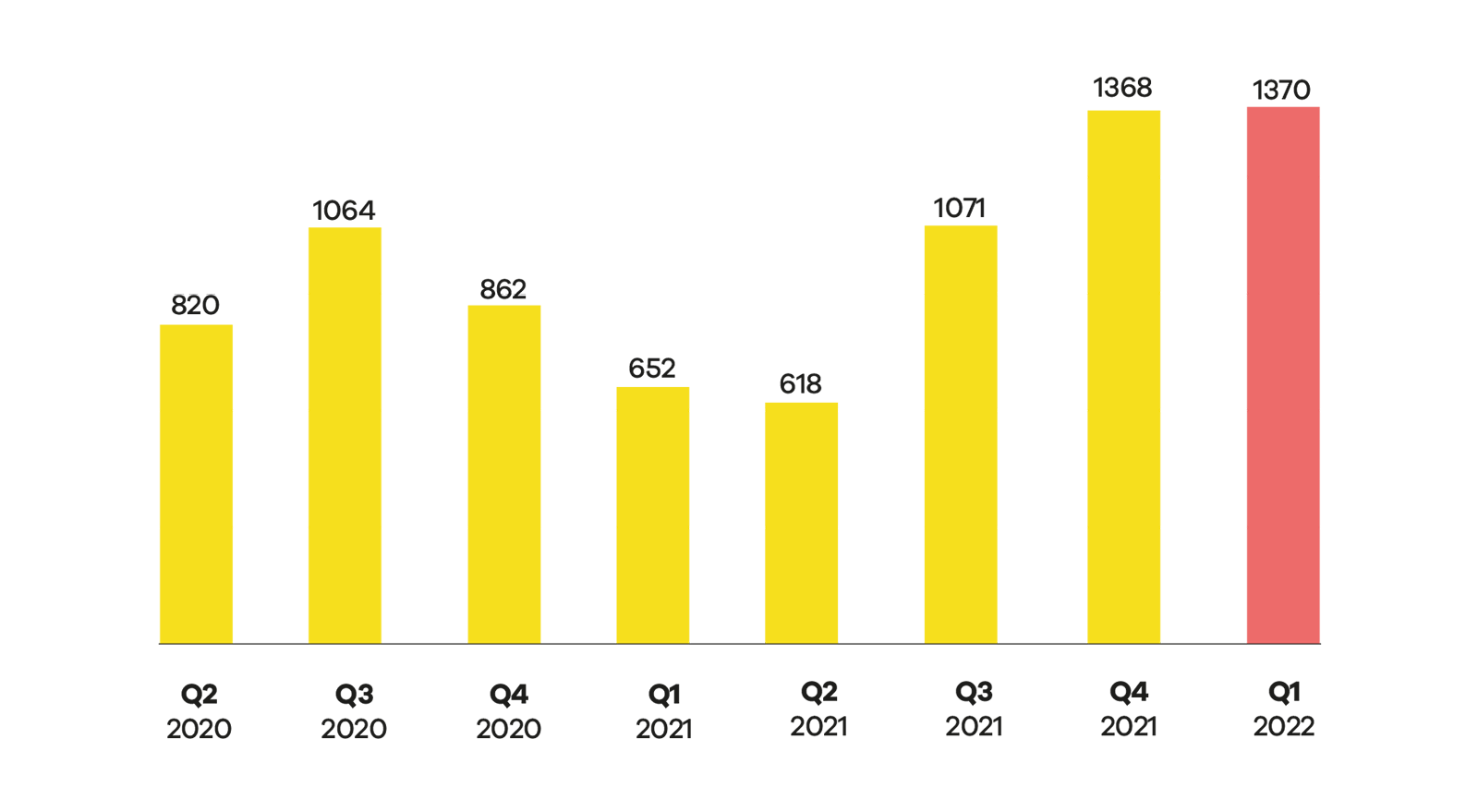
Phishing and credential harvesting remains the most reported incident category.
For more on the New Zealand threat landscape in Q1 2022, see The CERT NZ Quarter One: Data Landscape.
Focus Area: The biggest catch
Phishing and credential harvesting is consistently the most reported incident category to CERT NZ, making up 59% of reports this quarter. On average, CERT NZ receives 73% more reports about this category than any other.
Phishing and credential harvesting report numbers
What is phishing and why is it so common?
Phishing tries to mimic an authentic communication from a trusted source, usually through email or SMS. The intent is to try to trick the recipient into taking an action, like clicking on a link or providing personal or financial information.
What CERT NZ is seeing
Phishing has evolved from the infamous ‘Nigerian Prince inheritance’ emails to far more plausible communications pretending to be from well-known brands and organisations.
Case Study: How phishing campaigns can lead to tech-scam calls
Phishing leads to tech-scam calls
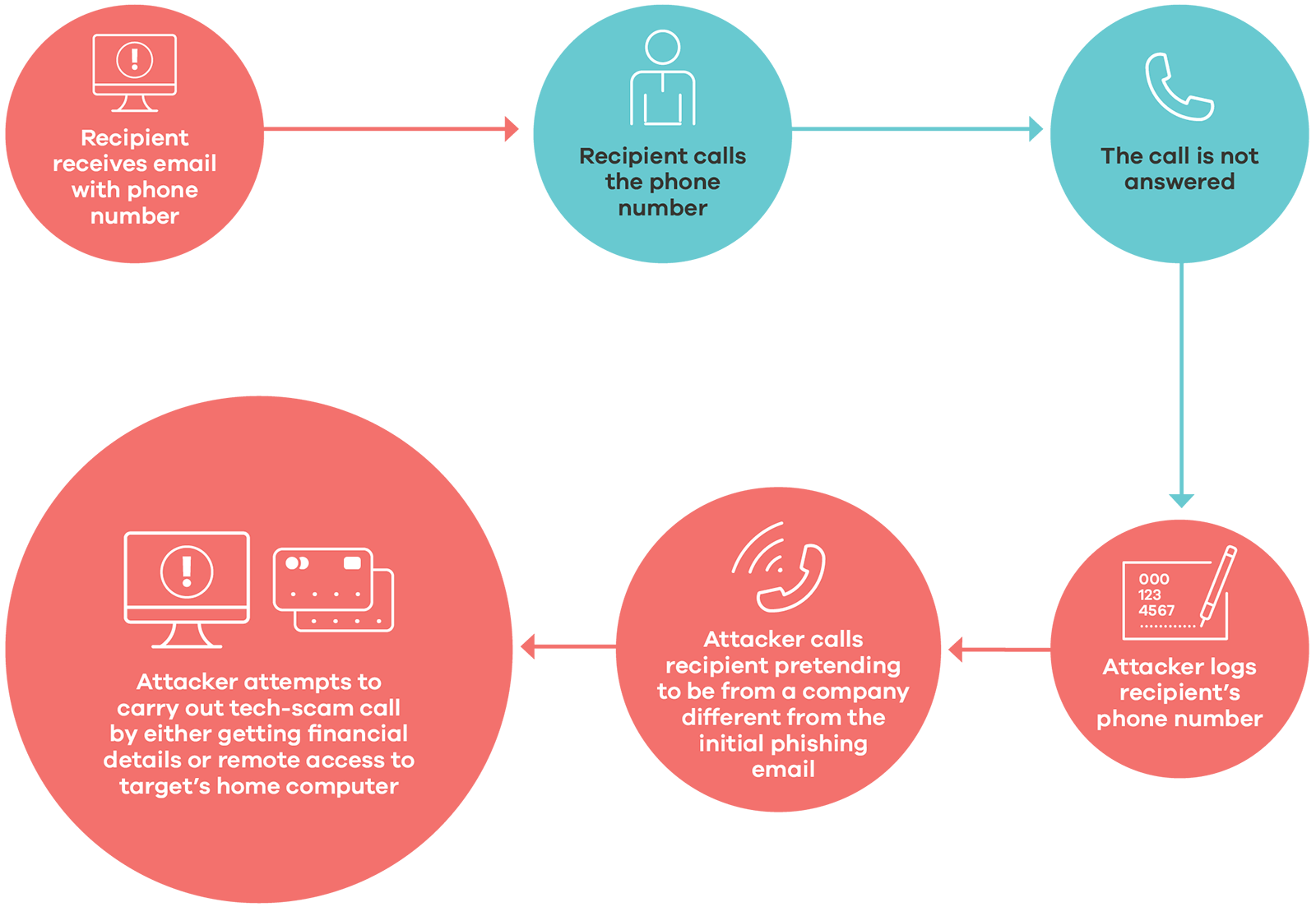
Phishing and credential harvesting are precursors to other cyber attacks. In quarter one, a phishing campaign distributed by both email and text, prompted recipients to call a number to cancel an expensive anti-virus subscription before being charged a significant sum the following day.
Received a tech-scam call?
- Banks and legitimate organisations don’t ask for personal or financial information over the phone nor request remote access. If you receive a call requesting these things, it’s likely a scam. Don’t provide any personal or financial information over the phone or allow the caller to have remote access to your PC or device.
- If you think the call is legitimate, you can decline to respond and then call the company yourself using the contact number listed on the company’s official website.
CERT NZ advice and mitigations
Phishing campaigns are always evolving, however advice to help protect against them remains the same
Report it.
If you suspect that you may have received a phishing attempt, or have fallen victim to a phishing scam, you can report it to CERT NZ.
Insight: NFTs
Techniques that attackers use are constantly evolving to reflect people’s interests and where they’re spending their money. An example of this is the increasing reports related to non-fungible tokens (NFTs) in quarter one.
Potential threats in the NFT trading process
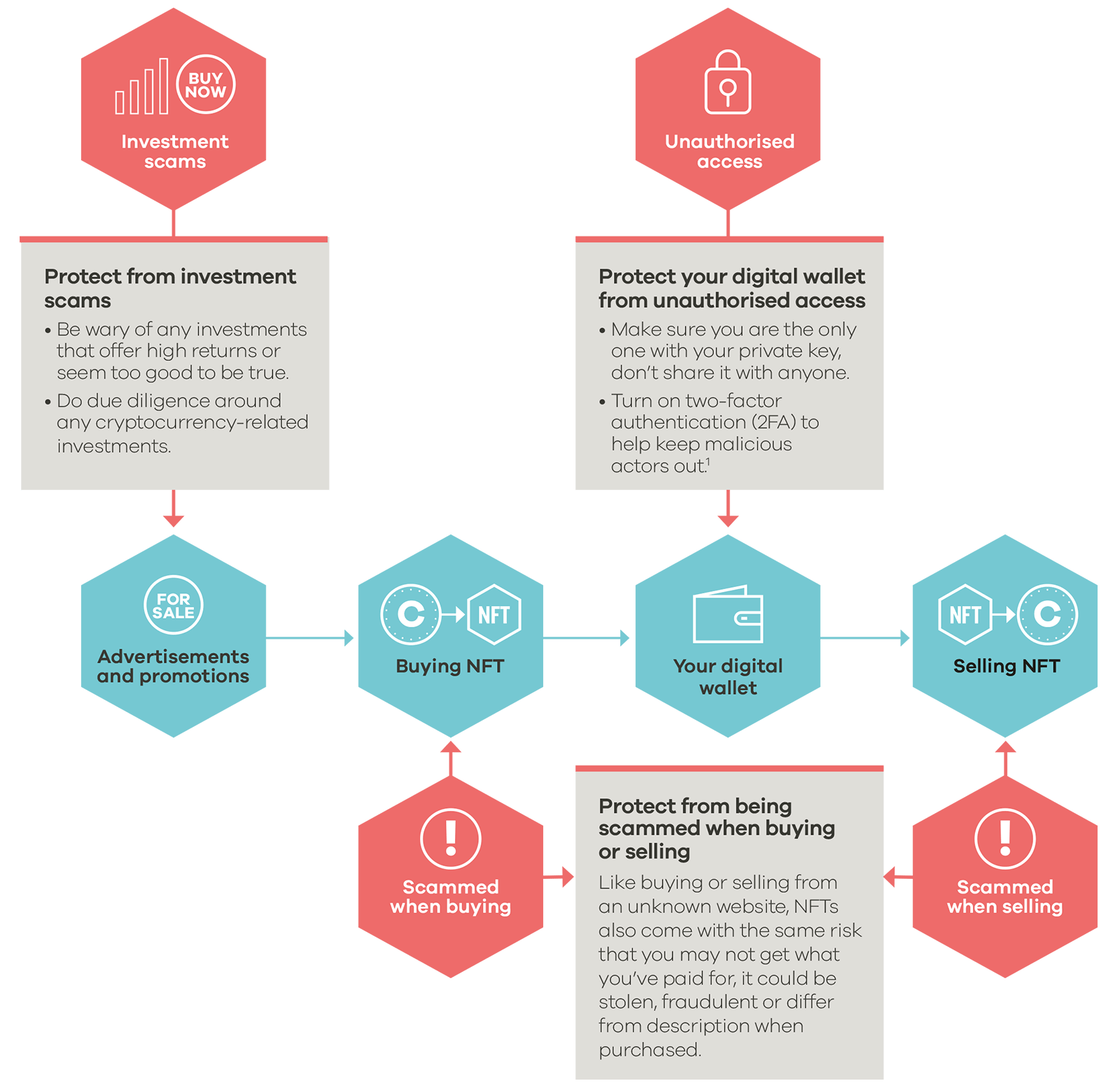
The Financial Markets Authority highlights three risks regarding cryptocurrencies
- They’re high risk and highly volatile, the price can go up and down very quickly.
- They’re not regulated in New Zealand.
- Cryptocurrencies, crypto-exchanges and the people using them are often the targets of hacking, online fraud and scams.
For more information go to the Financial Markets Authority's cryptocurrencies page.
Cryptocurrencies External Link
Insight: Ransomware attacks targeting network attached storage devices
CERT NZ received 17 reports about ransomware this quarter, five of which specifically targeted network attached storage (NAS) devices. These NAS-targeted ransomware attacks locked files on the device preventing the owners from accessing their information, like business files, family photos and more.
How to protect your NAS
- Prevent attackers gaining access by not exposing your NAS to the internet. If internet access is necessary, restrict it by IP/CIDR or geolocation.
Network segmentation and separation - Change default or weak passwords to long, strong and unique passphrases.
How to create a good password - Apply updates as soon as they are available.
Patching - Turn on two-factor authentication.
Use two-factor authentication to protect your account