Business
Explore our content to find practical guidance on how to keep your business safe and secure online.
Guide
Types of remote access software
There are different ways to remote into a system or computer. This guide will help you find the right one for your busin

News
Reserve Bank of New Zealand data breach
The Reserve Bank of New Zealand has suffered a data breach which has been widely reported in New Zealand media. The bre
Alert
Investment scam websites increasing
Guide
Software as a service
Find out the pros and cons of using software as a service (SaaS) products and our advice on how to keep those accounts s

News
Dec signs off
Former CERT NZ Deputy Director, Declan Ingram was one of the founding members of CERT NZ. After four years, he has moved
Guide
Preventing your email from being spoofed
Configuring security controls for your business domain such as SPF, DKIM, and DMARC can help you prevent attackers from

News
COVID-19: operating your business under Alert Levels 3 and 2
From 11:59pm on Sunday the 14th of February Auckland is at Alert Level 3 and the rest of New Zealand at Alert Level 2.

Guide
Getting a vulnerability report
If someone finds a vulnerability in your service or product that could be exploited in an attack, make it easy for them

News
Technical guidance about communicating the COVID-19 vaccine rollout for workplaces
CERT NZ has put together best practice technical guidance on communicating the COVID-19 vaccine process to members of st

Guide
Creating an incident response plan
As a business you’ll know the importance of online systems in running your day-to-day operations, that’s why it’s import
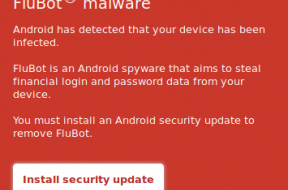
News
Text message scam infecting Android phones with FluBot
FluBot malware is spreading via links in text messages relating to parcel deliveries.

Guide
What to do after you’ve identified a cyber security incident
Responding quickly to a cyber security incident can reduce the impact on your business, but sometimes it’s difficult to

News
NCSC Advisory: Cyber threats relating to tensions between Russia and Ukraine
Due to the heightened tensions between Russia and Ukraine, the National Cyber Security Centre (NCSC) is encouraging New
Guide
Communicating in a cyber security incident
When your business experiences a cyber security incident, it’s easy to forget that responding to the technical issue is

News
Urgency, fear and opportunity used by cyber attackers to engineer responses
Following a record quarter at the end of 2021, reports of cyber incidents and the associated financial losses have dropp